ExternalName Service in Kubernetes: How It Works & When to Use It
Key Takeaways
- ExternalName services let Kubernetes apps reach external systems using normal service names, by mapping a Kubernetes service to an external DNS hostname instead of routing traffic to pods.
- They act purely as a DNS alias (CNAME), not a network proxy, which means Kubernetes does not provide load balancing, health checks, or port management for the external service.
- This abstraction helps keep application configuration consistent across environments, allowing teams to change external endpoints (like databases or APIs) without modifying application code.
- ExternalName services are often used for managed databases, third-party APIs, and hybrid-cloud migration scenarios, where dependencies still live outside the cluster.
- Teams need strong DNS reliability, security controls, and observability, otherwise connectivity issues or latency from external dependencies can be hard to detect and troubleshoot.
Modern cloud-native systems rarely exist in isolation. Kubernetes clusters often rely on databases, APIs, SaaS platforms, and legacy services running outside the cluster. According to the Cloud Native Computing Foundation, Kubernetes adoption continues to grow across enterprises, with 82% of container users leveraging Kubernetes, and 66% of AI initiatives are leveraging Kubernetes to scale their AI rollouts.
This creates a common challenge: how can applications inside Kubernetes reliably connect to services that live outside the cluster while maintaining consistent service discovery?
The ExternalName service in Kubernetes solves this problem. Instead of routing traffic to cluster pods, an ExternalName service maps a Kubernetes service to an external DNS name. This allows applications to reference external dependencies using the same internal Kubernetes service naming conventions.
In this guide, we’ll explore what an ExternalName service is, how Kubernetes DNS resolves it, when it should (and should not) be used, how to configure it with practical examples, and the best practices for production environments.
What Is an ExternalName Service in Kubernetes?
In Kubernetes, an ExternalName service is a special type of Kubernetes service object that allows applications inside a cluster to access resources hosted outside the cluster through Kubernetes-native service discovery. Instead of routing traffic to pods like most Kubernetes services, an ExternalName service maps a Kubernetes service name to an external DNS hostname. When a pod queries the service through Kubernetes DNS, the cluster DNS service returns a CNAME record pointing to the external domain, allowing the application to resolve and connect to that resource directly.
Key characteristics of an ExternalName service:
- Does not create endpoints or pods
- Resolves to an external DNS hostname
- Uses Kubernetes service metadata for discovery
- Works through the cluster DNS service
This allows applications inside Kubernetes to access external dependencies through a standard Kubernetes service name.
Example Architecture
Application Pod → Kubernetes Service → ExternalName → External API
This abstraction layer allows you to change the external endpoint without modifying application code.
ExternalName Service vs ClusterIP and Other Kubernetes Service Types
Kubernetes supports several service types that expose applications running inside a cluster. Each type routes traffic differently depending on whether the destination is internal, externally accessible, or located outside the cluster. An ExternalName service differs from traditional Kubernetes services because it does not route traffic to pods. Instead, it maps a Kubernetes service name to an external DNS hostname. The table below summarizes the most common Kubernetes service types and when they are typically used:
Unlike other service types that act as network proxies for pods, an ExternalName service simply creates a DNS alias pointing to an external resource. This makes it useful for integrating services that run outside the Kubernetes cluster.
Key Differences Between Kubernetes Service Types
ClusterIP
- Routes traffic to pods inside the cluster
- Uses components such as kube-proxy or iptables for routing
- Commonly used for internal microservice communication
ExternalName
- Does not proxy or route traffic through Kubernetes
- Creates a DNS alias to an external service hostname
- Useful for connecting to external APIs, databases, or services
LoadBalancer
- Requires a cloud provider load balancer
- Used to expose services to external internet traffic
- Common for public APIs or web applications
ExternalName services are particularly helpful when applications depend on external infrastructure such as managed databases or third-party APIs, while still maintaining consistent Kubernetes service naming.
How the ExternalName Service Works in Kubernetes DNS
Kubernetes includes a built-in DNS system that automatically creates DNS records for services and pods, allowing workloads to communicate using predictable service names rather than dynamic IP addresses. When a standard Kubernetes service is queried, the cluster DNS service typically returns the IP address associated with that service. However, an ExternalName service behaves differently. Instead of resolving to an internal cluster IP, the DNS server returns a CNAME record pointing to an external hostname defined in the service configuration.
From the application’s perspective, the process still looks like a normal Kubernetes service request. A pod queries the service name through Kubernetes DNS, receives the external hostname as the response, and then resolves that hostname through standard DNS resolution. This allows applications inside the cluster to access external systems - such as managed databases or external APIs - while continuing to use familiar Kubernetes service names for discovery.
Common Use Cases for an ExternalName Service in Kubernetes
ExternalName services are commonly used when applications inside a Kubernetes cluster must communicate with systems running outside the cluster boundary. Instead of embedding external hostnames directly in application configuration, teams can expose those dependencies through a Kubernetes service abstraction. This allows workloads to reference external systems using familiar Kubernetes service names while maintaining flexibility in how those dependencies are managed. Below are several common scenarios where ExternalName services are particularly useful:
1. Connecting to Managed Databases
Many cloud-native applications rely on managed database platforms hosted outside the Kubernetes cluster. Instead of configuring database endpoints directly within application settings, an ExternalName service can expose the database through a Kubernetes service name.
Examples include:
- Amazon RDS
- Google Cloud SQL
- Azure SQL
Using this approach allows applications to reference the database through a consistent internal service name while infrastructure teams manage the actual database endpoint externally.
2. Accessing Third-Party APIs
Applications frequently depend on external APIs for capabilities such as payments, authentication, or analytics. An ExternalName service can act as a stable service abstraction that points to the external API endpoint.
Common examples include:
- Payment processing services
- Authentication providers
- Analytics or monitoring platforms
By routing requests through a Kubernetes service name, teams can maintain consistent service discovery across different environments.
3. Multi-Environment Service Abstraction
ExternalName services can also simplify configuration across development, staging, and production environments, and are useful in hybrid-cloud setups. This is increasingly relevant as cloud-native infrastructure expands, with recent CNCF research showing that around 30% of developers operate in hybrid cloud environments and about 23% use multi-cloud deployments.
While the external endpoints may differ between environments, applications can reference the same Kubernetes service name.
In this setup, applications always connect to:
database-service
The ExternalName configuration determines which external endpoint is used in each environment, allowing infrastructure teams to change dependencies without modifying application code.
How to Create and Configure an ExternalName Service
Creating an ExternalName service in Kubernetes involves defining a service manifest where the service type is set to ExternalName and the configuration points to an external DNS hostname. Unlike standard Kubernetes services that route traffic to pods using selectors and endpoints, an ExternalName service functions purely as a DNS alias within the cluster.
When the manifest is applied, Kubernetes registers the service with the cluster DNS system. Any workload inside the cluster can then reference the service using a normal Kubernetes service name, while the DNS system resolves it to the specified external resource. This approach allows applications to connect to external APIs, databases, or services without embedding external hostnames directly in their configuration.
Defining an ExternalName Service Manifest
To create an ExternalName service, you define a Kubernetes service manifest where the service type is set to ExternalName and specify the external DNS hostname the service should resolve to. Unlike typical services that route traffic to pods, this configuration simply creates a DNS alias within the cluster that points to an external endpoint.
Below is a basic example of an ExternalName service manifest.
Key fields explained
Once applied, the service becomes available inside the cluster.
Apply the manifest:
Example output
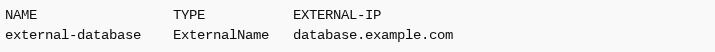
Next, test DNS resolution from inside a running pod to confirm the service resolves correctly within the cluster.
If the hostname resolves correctly, the cluster DNS service is returning the expected CNAME record, and workloads inside the cluster can access the external service using the Kubernetes service name.
Accessing External Endpoints Through an ExternalName Service
Once an ExternalName service is configured, applications inside the Kubernetes cluster can access the external resource using the Kubernetes service name, just as they would with any internal service. The underlying DNS resolution ensures that requests are automatically directed to the external hostname defined in the service configuration.
For example, an application can reference the service in its configuration like this:
In this setup, the application does not need to know the actual external hostname. Kubernetes DNS resolves the service name and routes the request to the correct external endpoint.
This approach provides several advantages:
- Configuration portability across environments
- Environment consistency when external endpoints differ between deployments
- Service abstraction, allowing infrastructure teams to update external dependencies without changing application code
Practical Examples of Using an ExternalName Service
ExternalName services are often used to simplify access to external infrastructure that applications depend on. A common example is connecting a Kubernetes workload to a managed database hosted outside the cluster. By creating an ExternalName service, the application can reference the database using a Kubernetes service name while the DNS system resolves the request to the external endpoint.
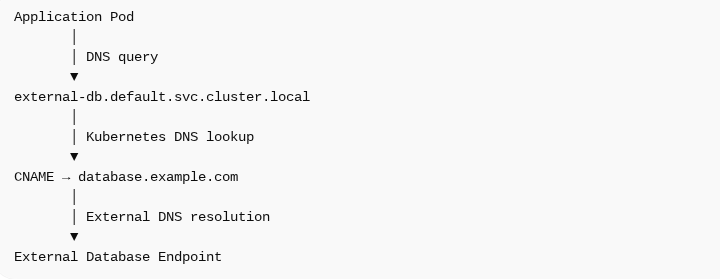
Example Architecture
Application request flow:

The ExternalName service acts as a DNS alias within the cluster.
Migration Patterns Using an ExternalName Service for External Dependencies
ExternalName services are commonly used during infrastructure migrations when applications still depend on systems that remain outside the Kubernetes cluster. This is especially relevant as many organizations operate hybrid environments - recent industry research indicates that about 87% of organizations run cloud-native workloads in hybrid cloud setups. By introducing an ExternalName service, teams can create a stable Kubernetes service name that points to the external dependency while the migration is underway. This allows applications to reference the service consistently without embedding external hostnames directly in their configuration.
Example Migration Workflow
- The application initially connects to an external database outside the cluster.
- An ExternalName service abstracts the external database endpoint.
- The database is later migrated into Kubernetes or the internal infrastructure.
- The service is updated from ExternalName to ClusterIP.
Because the application always uses the same Kubernetes service name, the migration can occur without changing application code.
Benefits
- Simplifies infrastructure transitions
- Reduces configuration changes
- Supports gradual modernization
This pattern is often used when migrating from legacy systems or monolithic architectures to Kubernetes-based microservices environments.
Security and Networking Considerations for an ExternalName Service
While ExternalName services simplify connectivity to external systems, they also introduce security and networking considerations. Because these services function as DNS aliases rather than Kubernetes-managed endpoints, traffic flows directly from the application to the external resource. As a result, teams must carefully manage DNS resolution, outbound access, and secure communication when integrating external dependencies.
Key Networking Considerations
- DNS Security: ExternalName services rely entirely on DNS resolution. If DNS records are compromised or misconfigured, traffic could potentially be redirected to unintended endpoints.
- Network Policies: Kubernetes network policies primarily control communication between pods inside the cluster and may not fully restrict outbound traffic to external services.
- TLS Encryption: External services should be accessed using encrypted protocols to protect sensitive data and ensure secure communication between applications and external resources.
Observability and Troubleshooting for ExternalName Service Connectivity
Troubleshooting ExternalName service connectivity can be challenging because traffic bypasses many of the typical Kubernetes networking layers. Since the service acts as a DNS alias rather than a proxy to pods, issues may originate from DNS resolution, external network conditions, or the external system itself.
Common issues include:
- DNS resolution failures
- Latency from external networks
- Misconfigured external endpoints
- Outbound networking restrictions
Troubleshooting Checklist
When diagnosing connectivity issues, teams typically verify the following:
Verify the Service Configuration
Check DNS Resolution
Test Network Connectivity
External dependencies can also introduce monitoring blind spots. Because traffic leaves the cluster, traditional Kubernetes service metrics may not capture interactions with external systems, making observability tools important for diagnosing latency and connectivity issues.
Limitations and Caveats of Using an ExternalName Service
Although ExternalName services provide a convenient way to connect Kubernetes workloads with external dependencies, they also come with several limitations. Unlike traditional Kubernetes service types, ExternalName services do not manage traffic routing, load balancing, or endpoint health. Instead, they function purely as DNS aliases that redirect service requests to an external hostname. Because of this simplified design, teams should understand the trade-offs before relying on ExternalName services in production environments.
Because of these limitations, ExternalName services should not be used for high-availability internal workloads.
Best Practices for Managing an ExternalName Service in Production Kubernetes Environments
Using ExternalName services in production environments requires thoughtful planning and operational awareness. Because these services rely entirely on DNS resolution and external infrastructure, teams must ensure that external dependencies are managed and monitored effectively. Establishing clear practices helps maintain reliability while minimizing potential issues related to connectivity, performance, or configuration changes. By following consistent operational guidelines, organizations can safely integrate external systems into Kubernetes-based applications.
- Use Clear Service Naming: Consistent naming conventions help teams quickly identify services that represent external dependencies and make troubleshooting easier.
- Document External Dependencies: Maintain clear documentation for external services, including endpoints, authentication requirements, and network access considerations.
- Monitor External Latency: External systems may introduce unpredictable latency due to network conditions or service availability, so monitoring performance is important.
- Implement Fallback Mechanisms: Applications should be designed to handle DNS failures, service outages, and connection timeouts gracefully.
- Use Observability Platforms: Monitoring and observability tools help identify connectivity failures, latency spikes, and dependency-related issues across distributed systems.
Deep Visibility Into ExternalName Service Dependencies With groundcover
ExternalName services introduce dependencies that exist outside the Kubernetes cluster, which can make monitoring and troubleshooting more challenging. Because requests leave the cluster and interact with external systems, traditional service metrics may not provide full visibility into performance or connectivity issues. Observability platforms help bridge this gap by providing deeper insight into application behavior and service dependencies. Solutions like groundcover enable teams to monitor how workloads interact with both internal services and external infrastructure.
This is how groundcover improves ExternalName service visibility:
- Unified Telemetry Collection: groundcover collects multiple types of telemetry from Kubernetes environments, including logs, metrics, traces, and Kubernetes events. This unified data allows teams to correlate application activity with infrastructure performance and quickly identify issues affecting external dependencies.
- Network Dependency Insights: By analyzing service interactions, groundcover helps identify external API calls, database latency, and relationships between services. This visibility makes it easier to understand how external dependencies impact application performance.
- eBPF-Powered Monitoring: groundcover uses eBPF-based telemetry to observe system and network activity at the kernel level. This approach provides detailed insights into traffic patterns and service interactions without requiring application-level instrumentation.
Conclusion
ExternalName services provide a simple and effective way to connect Kubernetes workloads with external dependencies. By mapping Kubernetes service names to external DNS records, they allow applications to maintain consistent service discovery without embedding external hostnames directly in configuration. This abstraction simplifies how applications interact with external databases, APIs, and other services outside the cluster.
At the same time, ExternalName services introduce considerations around observability, networking, and Kubernetes security. Because traffic bypasses typical Kubernetes service routing, teams must ensure external dependencies are properly monitored and managed. When implemented thoughtfully and supported by strong observability practices, ExternalName services can play an important role in modern hybrid and cloud-native architectures.


























.svg)